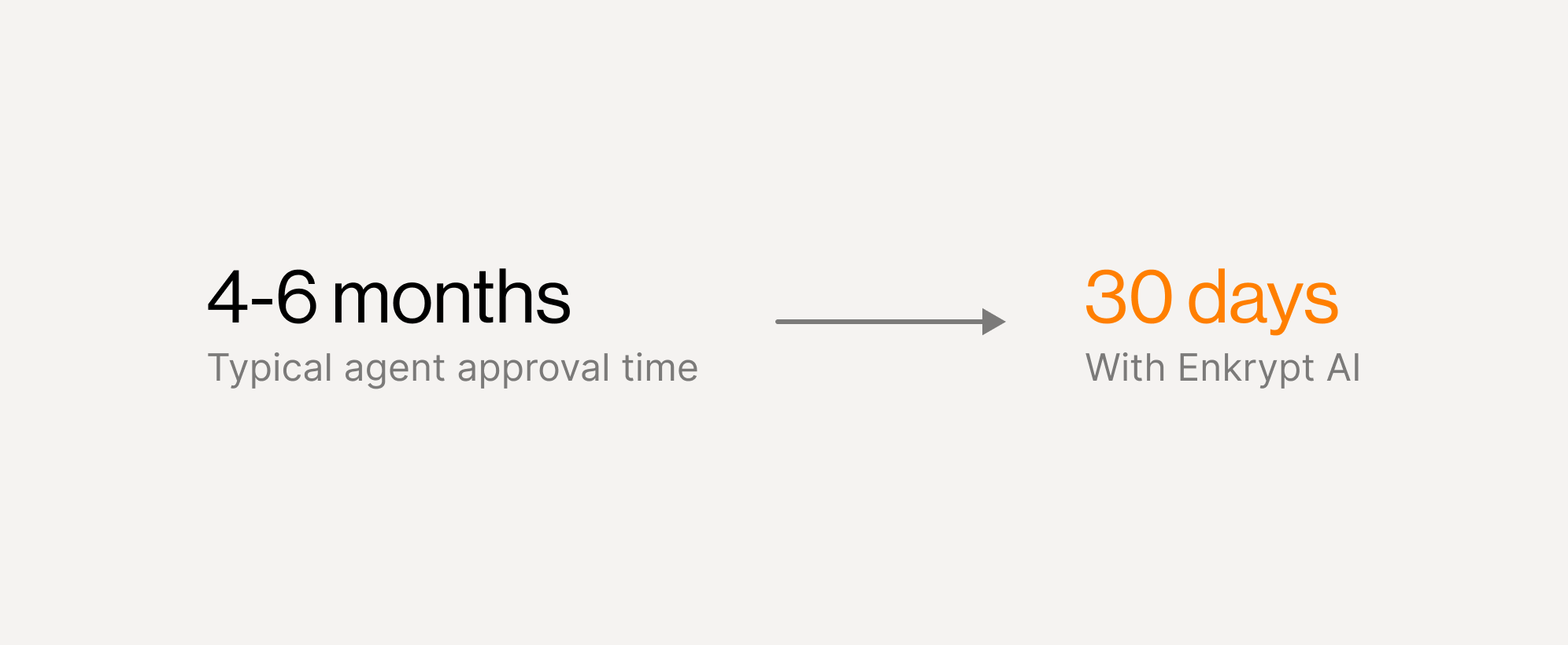
Get your AI agent approved and into production in 30 days
One forwardable Release Packet that gives Security, Legal, and Product everything they need to say yes — so you can ship fast.
Your agent works. But three teams won't approve it.
Most conversation agents don't fail because the model is bad - they fail because enterprises can't sign off on them.
One artifact that turns "launch risk" into signed approvals
Enkrypt AI produces an Agent Release Packet — a single, forwardable document that gives every stakeholder the evidence they need to approve your agent.
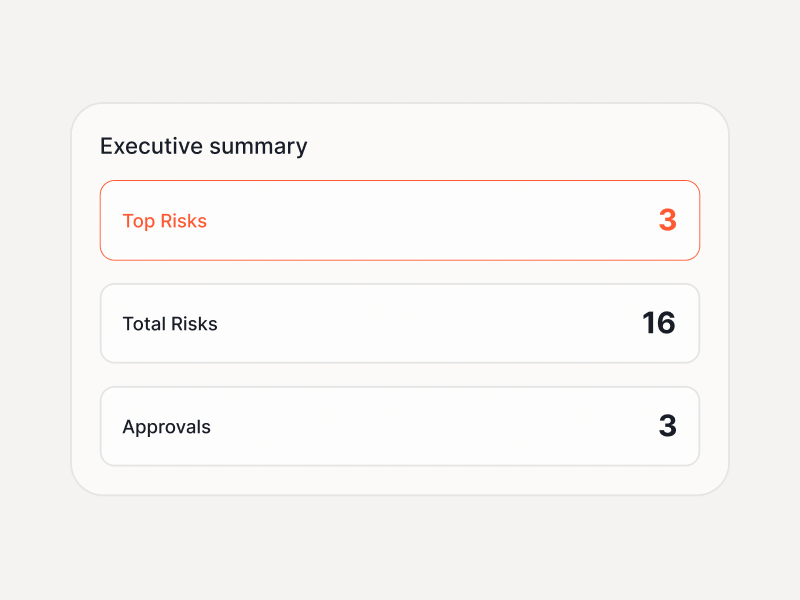
Top risks, approvals, launch blockers — one page for leadership
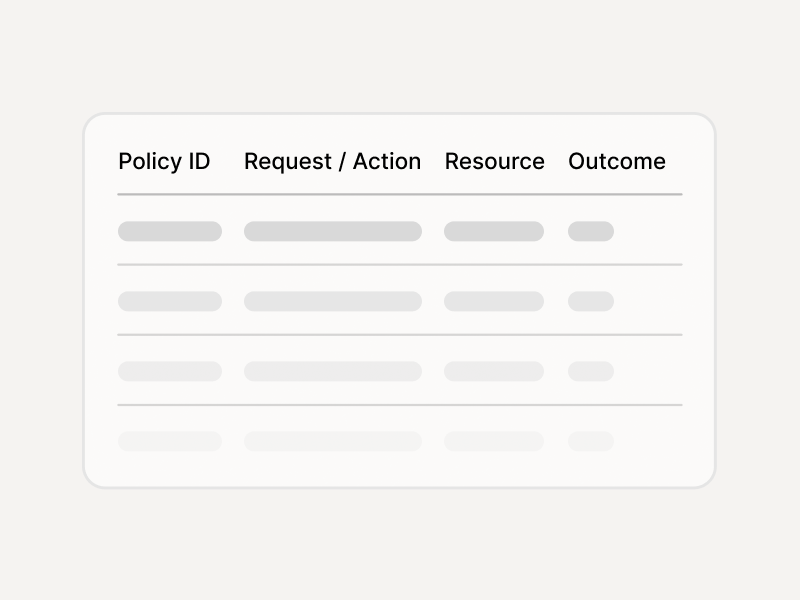
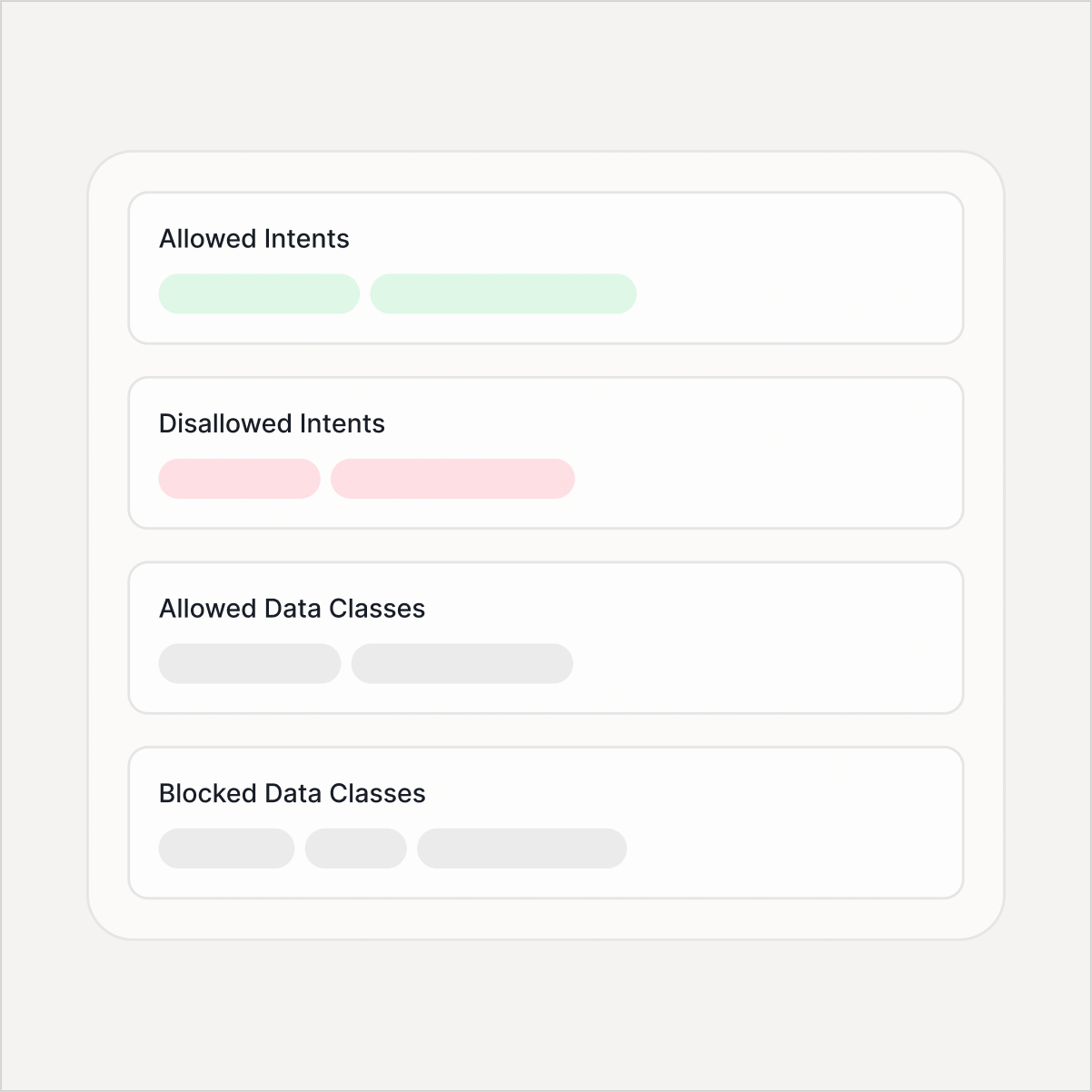
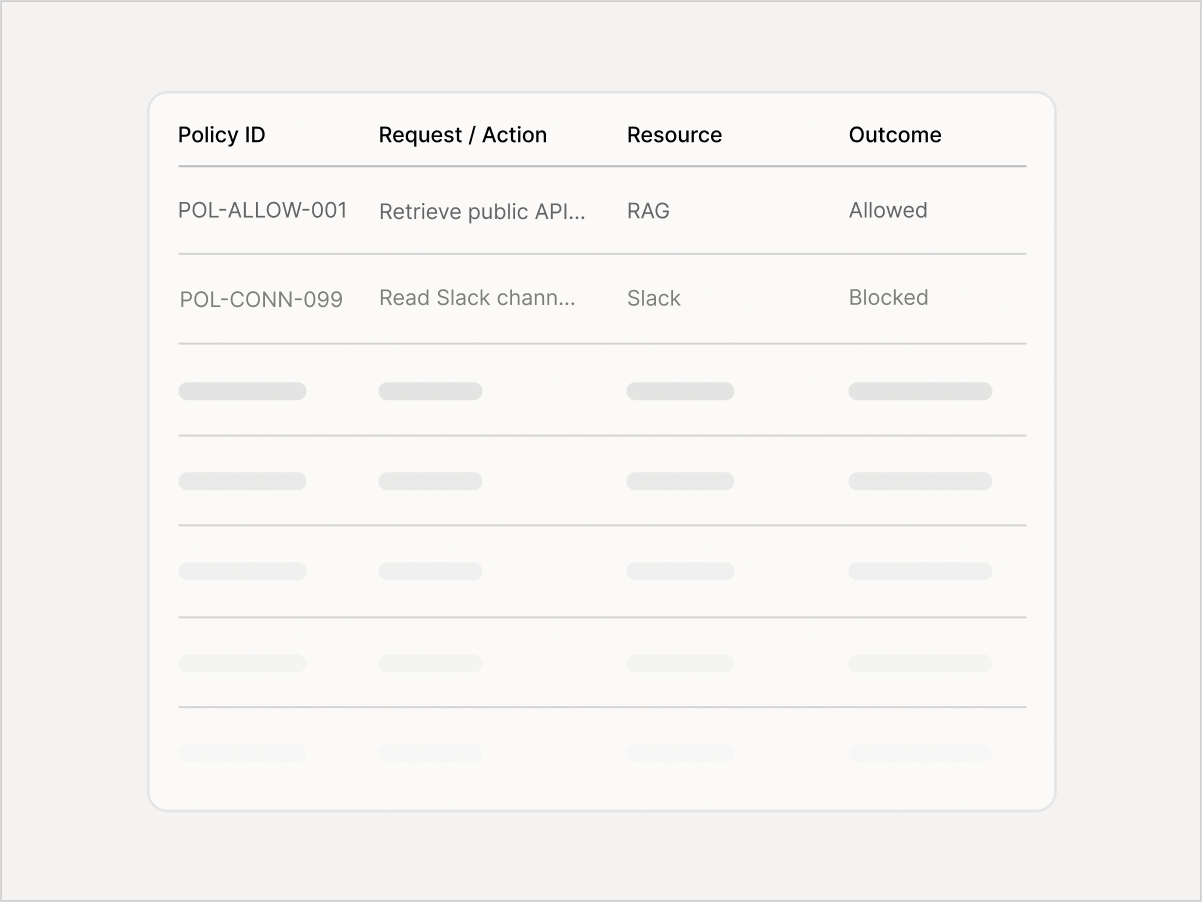
What's allowed, blocked, and requires approval — with policy IDs
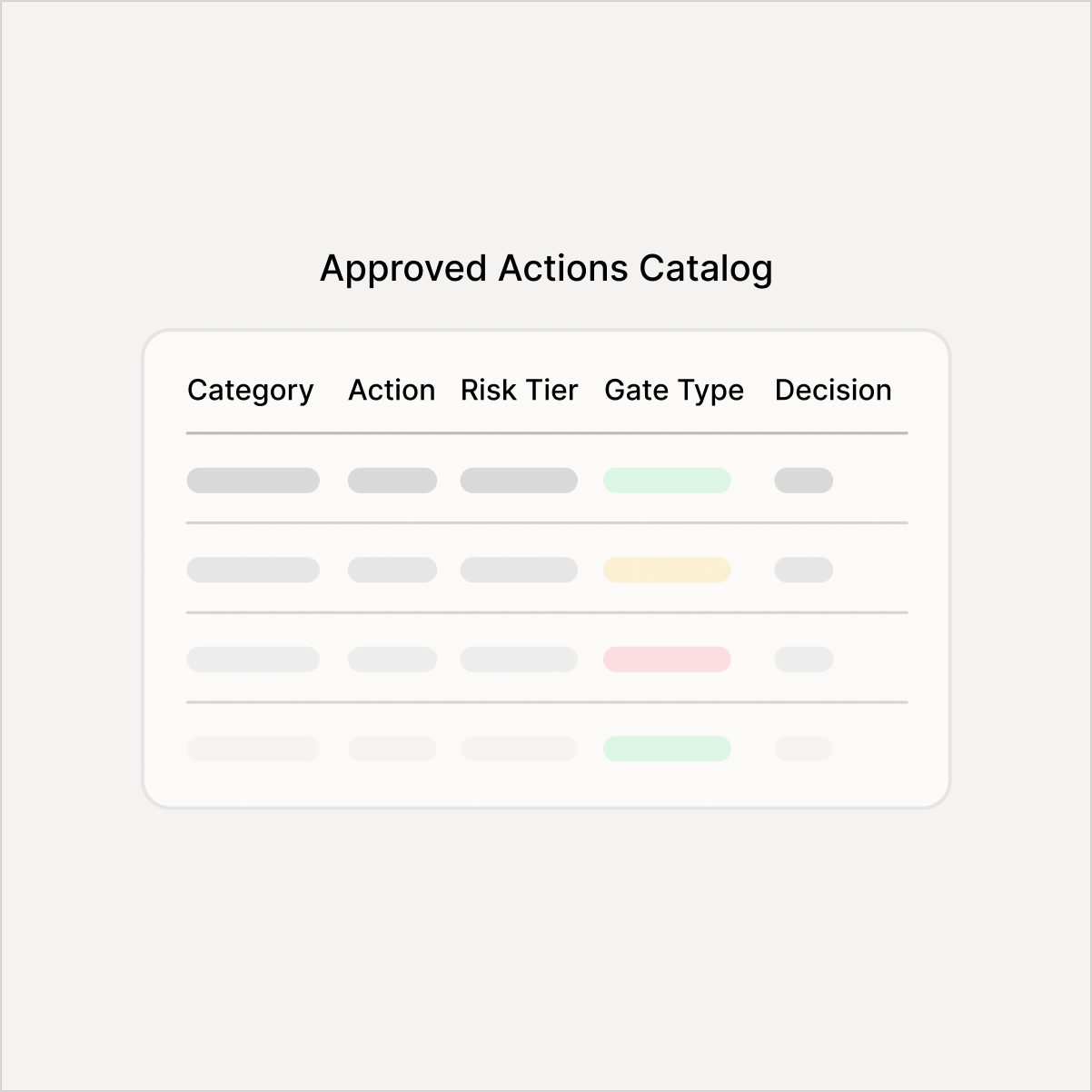
Every action risk-tiered with approval rules and owners

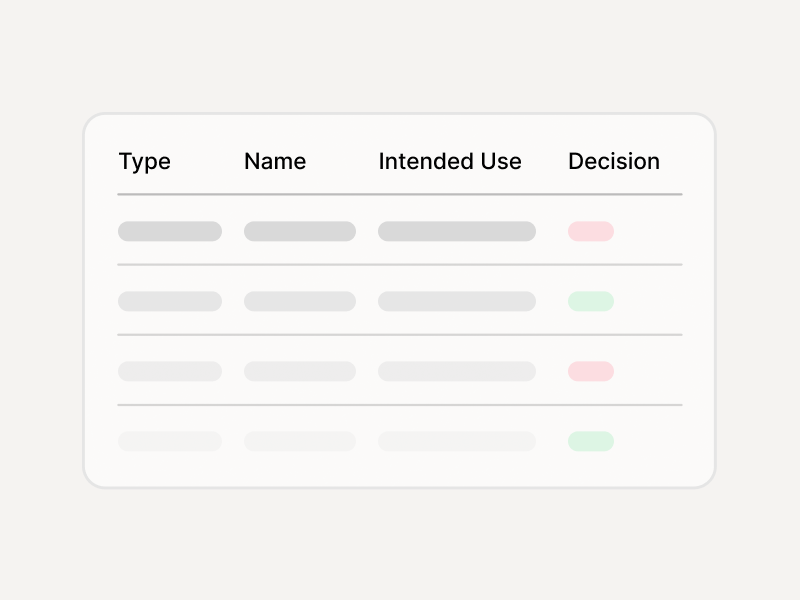
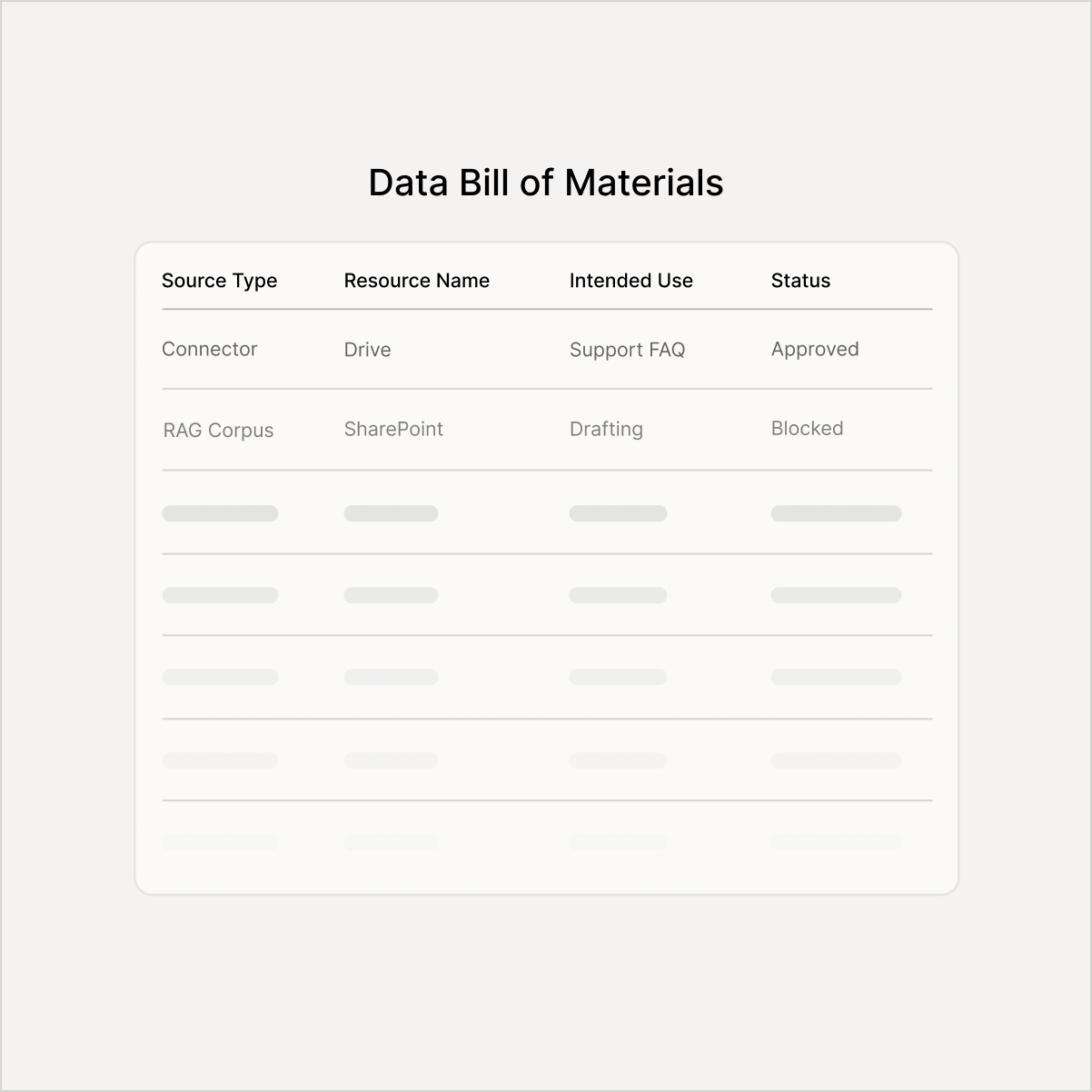
Connectors + RAG corpus approved or blocked by intended use
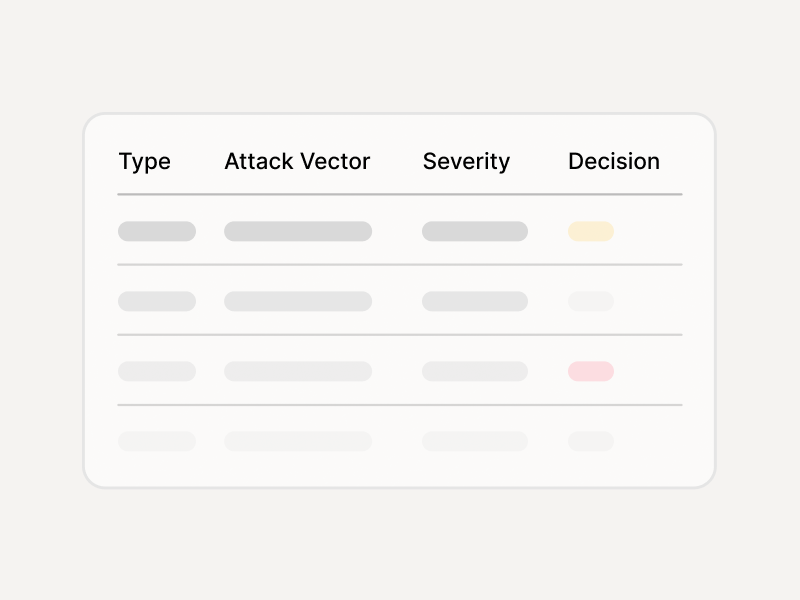
Test cases for jailbreaks, injection, and leakage — with pass/fail results
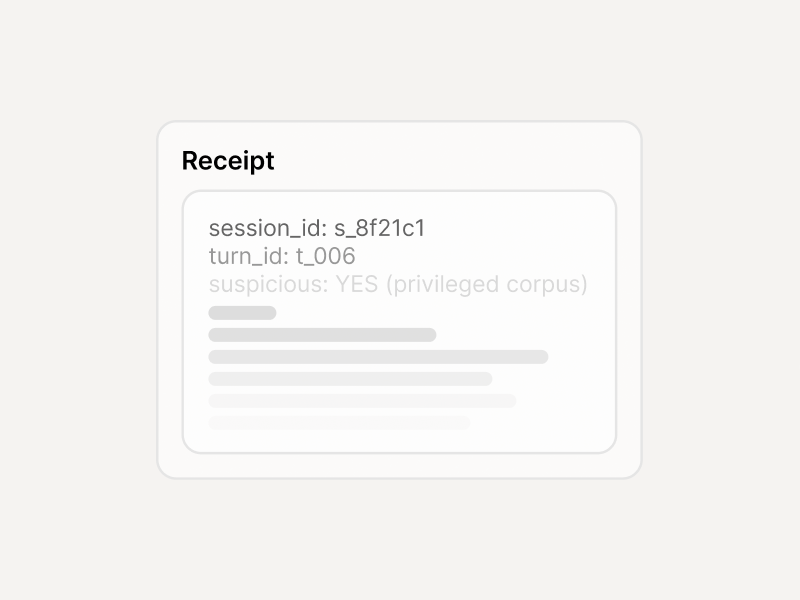
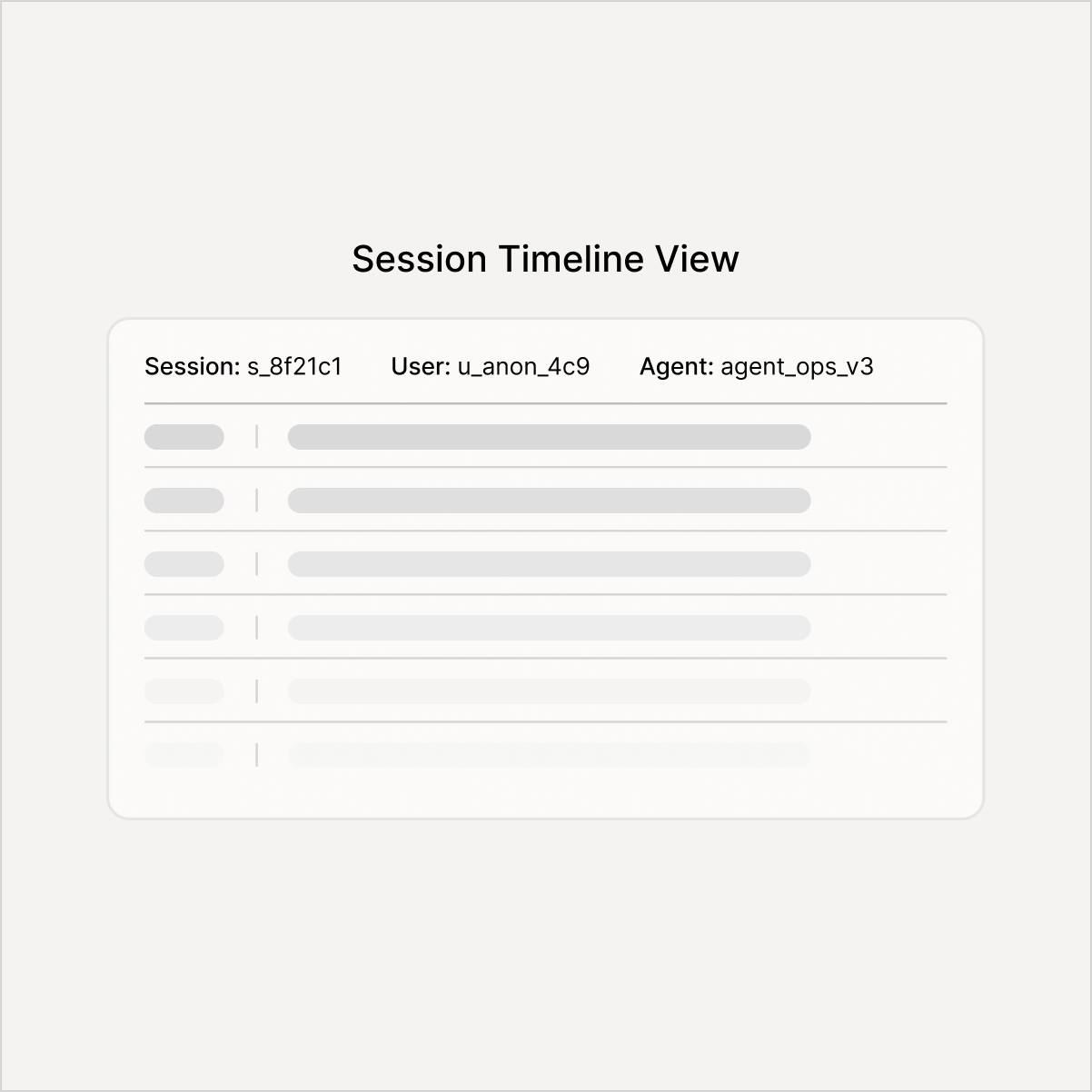
Decision logs, approval records, and incident export schema
What you get on Day 1 vs Day 30
Start building immediately. Ship with full approvals in a month.
Five steps from "blocked" to "approved"
Start with one agent and one environment. Repeat for every agent after that.

Six products, one workflow — reuse across every agent
Standardize once. Every new agent becomes a repeatable release, not a new security project.
Built for teams that ship to regulated industries
Audit-ready from day one. Plugs into the tools your teams already use.
Integrations
- Slack / Teams
- PagerDuty / Opsgenie

- Jira
- ServiceNow

- Splunk/ Sentinel/ Datadog
- Webhooks