Approve vendor AI in days, not weeks - and know when it changes
Replace questionnaire ping-pong with a Vendor Risk Packet, continuous drift monitoring, and a Renewal Memo you can forward — all backed by enforceable controls and evidence.
Procurement needs an AI risk decision before renewal
Security finds embedded AI with unclear data boundaries
Vendor changes models or connectors without notice
Your AI risk surface isn't just what you build. It's what you buy.
Model providers, copilots, embedded AI inside SaaS products, and third-party MCP servers your teams connect to — all introduce risk that questionnaires can't capture.
Static questionnaires capture what the vendor says today. But models, prompts, policies, and connectors change constantly — and your risk assessment doesn't update.
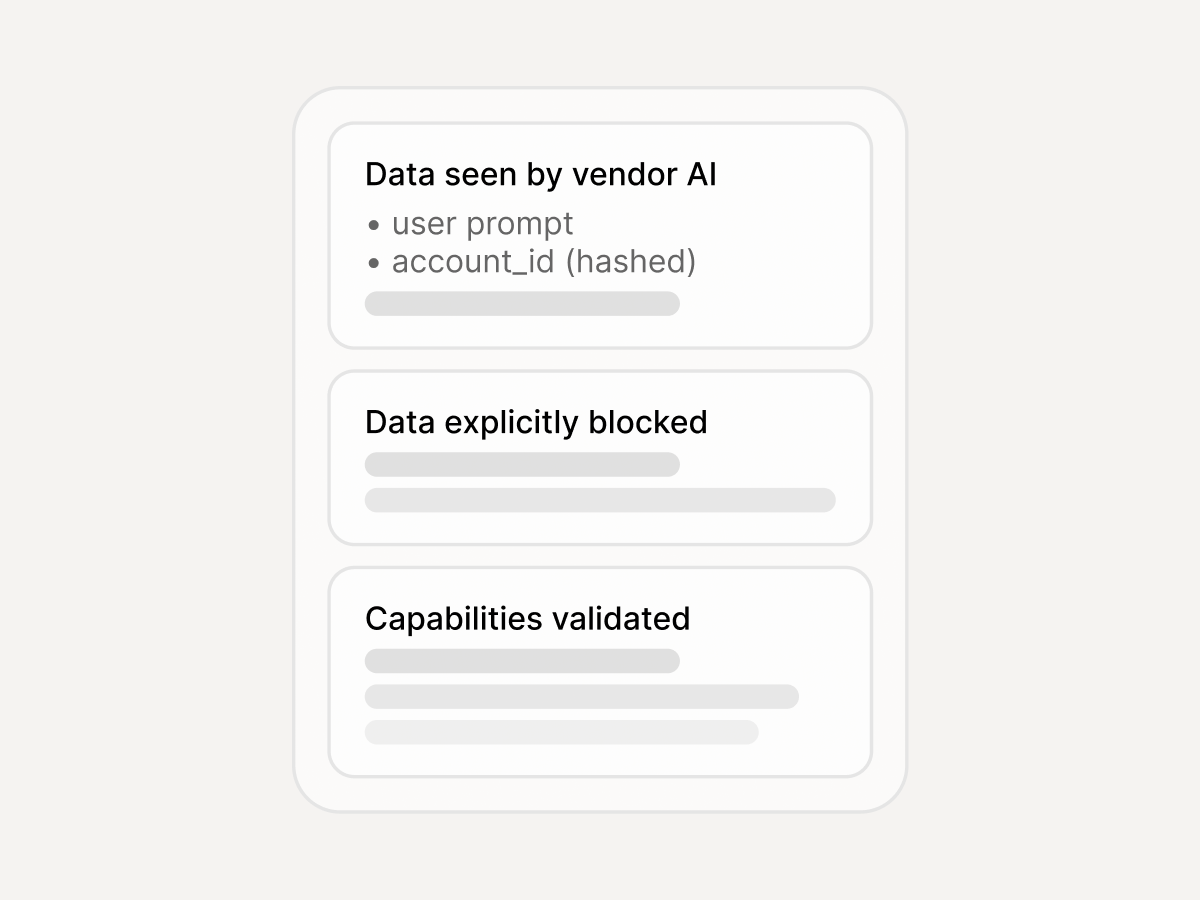
SaaS vendors ship AI features you can't inspect. You still need to know what data leaves your environment, what the model can produce, and who controls retention.
Without receipts and evidence, every renewal and incident review is a scramble. Teams dig through Slack and screenshots instead of exporting a packet.
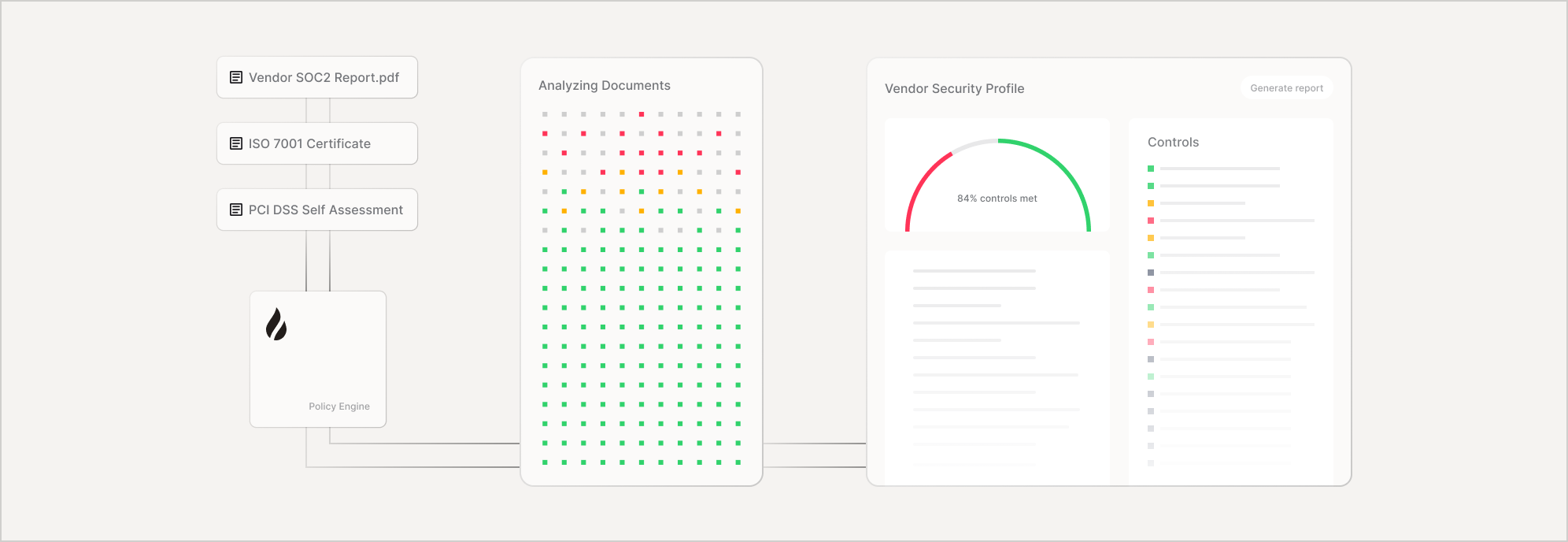
Assess before approval. Monitor drift. Operate with evidence.
Three stages that replace questionnaire cycles with enforceable controls and continuous visibility.

Three artifacts that replace questionnaire cycles
Circulate internally, keep current with drift monitoring, and walk into renewals with evidence.
Fits into your existing vendor review process
Six stages — from intake to renewal — with evidence generated at every step.
Vendor, feature, intended use, data boundaries
Risk tier + required controls from policy
Validate + generate Vendor Risk Packet
Approve / conditional / block with mitigations
Detect drift + update scorecards
Export Renewal Memo + Evidence Pack

Actions, not just alerts
When vendor behavior shifts, teams choose response options by risk tier — from scope restrictions to full blocks.
Limit by tenant, feature, data type, or geography until remediated.
Require human approval for high-risk actions or outputs before they execute.
Redact or minimize sensitive data before requests leave your environment.
Disable a specific MCP server, tool, or connector until the vendor remediates.
Auto-generate a memo with required mitigations for Procurement and Legal.
Automatically adjust vendor risk score and trigger reassessment workflows.
Built on Enkrypt AI products
Policy Engine at the center — governance policy becomes enforceable controls with receipts.
Integrations
Vendor risk evidence, alerts, and approvals flow into the tools your procurement, security, and GRC teams already use.
- Slack / Teams
- PagerDuty / Opsgenie

- Jira
- ServiceNow

- Splunk/ Sentinel/ Datadog
- Webhooks